-
-
Notifications
You must be signed in to change notification settings - Fork 233
PolicyEditor
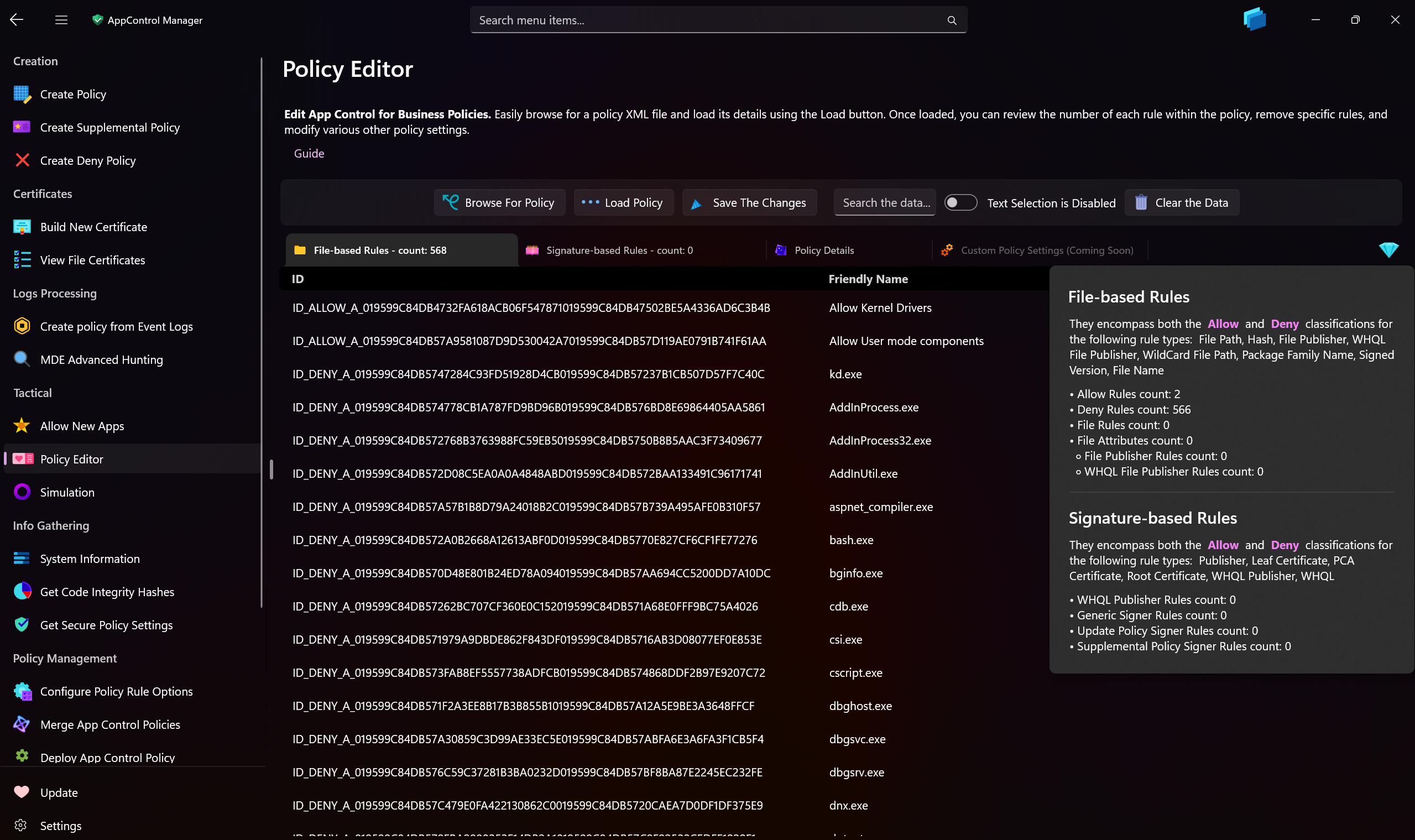
Leverage the Policy Editor page to effortlessly refine your App Control policy files. With this tool, you can remove individual rules or clear all rules in one action, while accurately displaying the count of each rule type. Seamlessly search for the rule you wish to modify, and easily update policy details such as name, type, version, policy ID info, type ID, base policy ID, and HVCI option level.
Eliminate the need for error-prone, manual editing in a text editor. When you modify App Control policies with the Policy Editor, your policy remains fully compliant with the Code Integrity schema throughout the process.
This feature also deduplicates any redundant rules or signers within the policy file.
Tip
You can use this feature to convert CIP binary files back to XML too.
-
Browse for Policy: Click this button to locate an App Control policy XML or CIP file. You can right-click or tap and hold on this button to preview the selected policy file.
-
Load Policy: Use this button to import the details of the chosen App Control policy into the user interface.
-
Save the Changes: Click this button to commit any modifications back to the selected App Control policy. If the file you are working with is a
CIPbinary policy, then using this button will save it as XML file with the same name in theAppControl Managerdirectory in Program Files (if the app is running elevated), or it will save the XML in the same location as the CIP file (if the app is running with standard privilege). -
Clear the Data: Use this button to reset all data loaded in the interface as a consequence of loading the policy.
-
Text Selection: Toggle this switch to enable or disable text selection within the List Views. When enabled, you can easily select and copy the text displayed in each cell.
-
Search the Data: Enter a keyword in this text box to quickly locate the specific rule you wish to edit.
-
Diamond-shaped button: Press this button to access additional information about the loaded policy, including the precise count of each rule type.
-
Policy Details Tab: In this tab, review and update the policy’s details such as Name, Policy ID, Base Policy ID, Version, HVCI Level, Type, and Policy ID Info.
-
Signature-based Rules Tab: This tab displays rules for the following levels: Publisher, PCA Certificate, Root Certificate, WHQL, WHQL Publisher, Leaf Certificate, Update Policy Signers, and Supplemental Policy Signers.
-
File-based Rules Tab: Here, you will find rules for various types, including Allow and Deny rules (e.g., Hash, PackagedFamilyName, or File Name levels), File Rules, SignedVersion level, File Publisher level, and WHQL File Publisher level.
Tip
Please note that the IDs shown in the List Views do not correspond to the current IDs in the XML file. Instead, they represent the IDs that will be incorporated once you press the "Save the Changes" button.
Note
The Policy Editor organizes each rule for effortless adjustments. For instance, File Publisher or WHQL File Publisher rules are segmented into individual File Attributes. Removing all File Attributes at a specific level will automatically eliminate the associated Signer and any related elements, ensuring your App Control policy remains clean and precise. In essence, a WHQL File Publisher or File Publisher level without any File Attributes effectively reverts to a Publisher or WHQL Publisher.
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Policy Editor
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Validate Policies
- View File Certificates
- Microsoft Graph
- Protect
- Microsoft Security Baselines
- Microsoft Security Baselines Overrides
- Microsoft 365 Apps Security Baseline
- Microsoft Defender
- Attack Surface Reduction
- Bitlocker
- Device Guard
- TLS Security
- Lock Screen
- User Account Control
- Windows Firewall
- Optional Windows Features
- Windows Networking
- Miscellaneous Configurations
- Windows Update
- Edge Browser
- Certificate Checking
- Country IP Blocking
- Non Admin Measures
- Group Policy Editor
- Manage Installed Apps
- File Reputation
- Audit Policies
- Introduction
- How To Generate Audit Logs via App Control Policies
- How To Create an App Control Supplemental Policy
- The Strength of Signed App Control Policies
- How To Upload App Control Policies To Intune Using AppControl Manager
- How To Create and Maintain Strict Kernel‐Mode App Control Policy
- How to Create an App Control Deny Policy
- App Control Notes
- How to use Windows Server to Create App Control Code Signing Certificate
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- System Integrity Policy Transformations | XML to CIP and Back
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
